Understanding DNS Over HTTPS - DoH
By Stacie Hoffmann
DNS over HTTPS (DoH) is a protocol recently released by the Internet Engineering Task Force (IETF). The protocol not only restructures the Internet ecosystem by concentrating data aggregation with big tech companies like Google but is slated to increase user responsibility and likely lead to further data abuse. These changes are hidden away from the average Internet user’s view, and are happening with no appropriate oversight or accountability structure in place.
The most talked about new protocol
The IETF is an open standard development organisation (SDO) focusing on Internet architecture. This group of engineers develops the Internet’s next generation of protocols. DoH is currently one of the IETF’s most talked about, and controversial, protocols. Not only does DoH change a basic architectural element of the Internet (namely the domain name system resolution mechanism), but it exemplifies the intersection of technology and policy.
Since the Snowden revelations, the SDO is noted for its increasing use of encryption in protocols for ‘privacy’ purposes. In reality, this equates to a form of data protection. However, employing encryption in Internet protocols like DoH also changes our expectations of key stakeholders in the Internet governance ecosystem. In light of this, Mozilla (who originally proposed the protocol), Cloudflare (Mozilla’s contracted DoH resolver), and Google are coming under increasing pressure from other stakeholders to slow down and rethink their deployment models.
What is DoH?
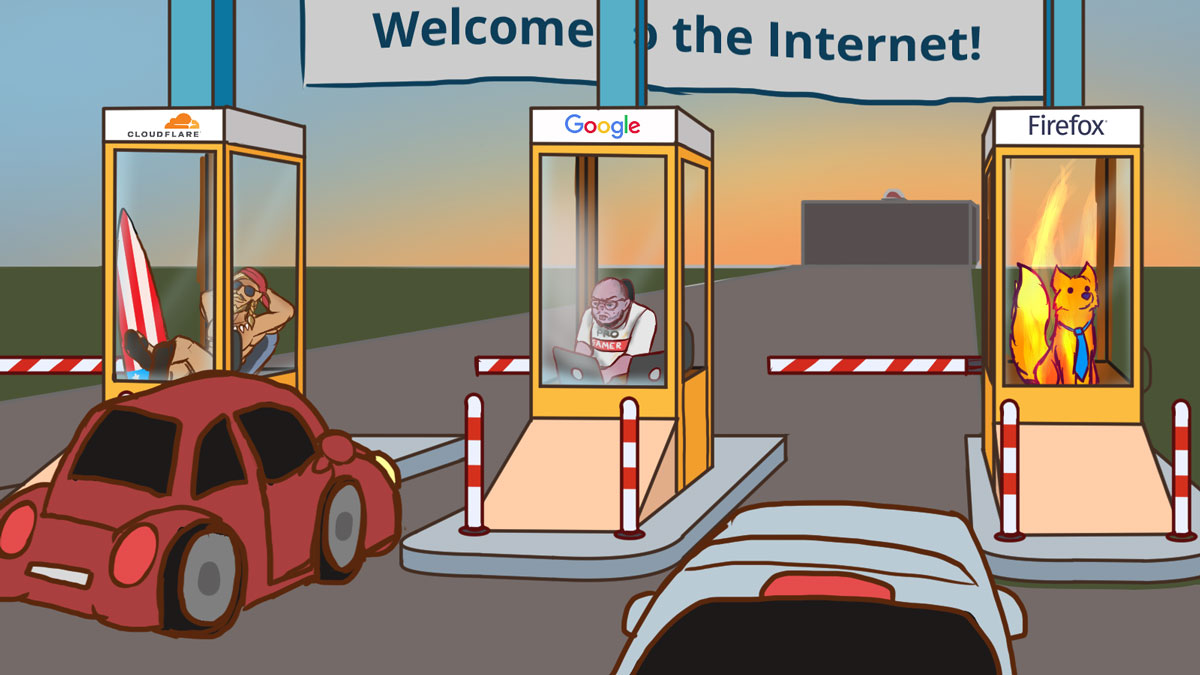
So, what is DoH and how does it change the Internet? 'DNS' stands for domain name system. The 'system' is a globally coordinated, decentralised network of servers that translate (i.e. resolve) user-friendly domain names (e.g. BBC.com) to numerical Internet Protocol (IP) addresses. At a basic level, this enables us to find ‘places’ and information in cyber space – in other words it’s how we find cat videos on the web. DoH changes this model, concentrating DNS resolution within the application layer (e.g. Mozilla/Cloudflare and Google) instead of the network layer (e.g. internet service provider (ISP) or DNS root server).
Moving DoH to the application layer effects cyber security, Internet consolidation, and public policy issues — creating more problems than it solves. In General Data Protection Regulation terms, any browser or app that adopts DoH (e.g. Google) is a data controller of personal data (DNS queries). The app will have access to and decision over how the data is processed and used. This doesn’t offer users more privacy, but instead changes their relationship with and expectations of apps using DoH – a relationship that is already largely abused for financial gain, built on problematic terms of service agreements, and layered within a complex global market system.
Key points
While I won’t go into detail on the technical side of DoH, there are two key points I will highlight:
- DoH changes a foundational trust model of the Internet; and,
- It impairs basic cyber security measures in the network layer that are effective and wide-spread.
For instance, many ISPs and organisations use their unique access to traffic data to protect users and businesses from malware and IP spoofing or block illegal content like child pornography. But with DoH’s encryption and resolution at the application layer, those protections at the network layer are not implementable.
And while we are encrypting all the ‘good’ traffic, we are also encrypting the ‘bad’ traffic. This has already been seen in the first malware to exploit DoH, Godlua, which encrypts the communication channel between the bots and web server. The likelihood of applications and devices opportunistically implementing DoH, and adopting the bad behaviours it enables, for their benefit is a clear and present danger.
In terms of public policy, a few of the issues include:
- Jurisdiction (e.g. the current resolvers are all incorporated in the US)
- Oversight and accountability (e.g. to users and national laws and regulation)
- Competition (e.g. further concentrating power with a few big tech firms)
- Non-discrimination principles (e.g. Net Neutrality)
- Pushing content (e.g. advertisements and content not requested by the user)
- User protection requirements (e.g. from malware, spam, IP spoofing, and illegal content like child pornography)
- Enables new data abuses and GDPR compliance issues (e.g. data aggregation and analysis)
- Potential for human rights infringement (e.g. invasion of privacy, data abuses, and impairing access to information)
There are additional issues created for network operators (e.g. ISPs) such as network management and customer service but that could use an article of its own. This being said, the alternate trust model and use of encryption may offer some benefits in specific use cases, so don’t throw the baby out with the bath water just yet. For instance, apps that would benefit from high integrity communications – such as for banking or medical use – could be protected from man-in-the-middle attacks and have greater oversight over who is connecting and using their service. In areas where governments are known for using DNS data to infringe on human rights online, encrypting DNS queries and using alternate resolvers can offer users more protection from traffic interception – but other protocols like DNS over TLS (DoT) also offer this service without the same wide-spread side effects. Effective implementation of these use cases all depend on the business model, appropriate oversight, and our trust in the app (e.g. Google) and DoH resolver (e.g. Cloudflare). The flexibility of the DoH protocol leads to lack of clarity in the business and trust models and contributes to the polarisation of the debate. There are unresolved technical issues, like resolver discovery, that the IETF plans to work on next. But this is not likely to take into account the potentially serious policy and human rights issues – which are not, nor should they be, the responsibility of engineers.
What about user choice?
However, recent discussions show some parties turning their attention towards users. There is a growing position among some in the IETF that user choice of DNS and DoH resolvers will solve the policy issues. Moving to DoH should definitely be an opt-in (rather than opt-out) change for users. However, the idea of user consent in the digital age is already a well-known riddle abused by tech companies. On top of this, we are asking users like our parents and children to have a deep understanding of three complex topics:
- The Internet’s architecture
- Responsibilities of stakeholders
- Business models and user contracts
Choice and transparency for users is a great start, but how would this be implemented? How much to users really understand the DNS?
Google is one of 8 companies that currently resolves half of global Internet traffic. It also corners the global market with 70% of Internet browsing traffic through its Android operating system and Chrome browser. How much of a ‘choice’ do users actually have?
We need more engagement
Understanding trade-offs is essential when developing new technology. We should question a technology being built on the premise of informed consent while minimising the issues it creates for cyber security and wholly turning it back on the public policy issues.
Appropriate oversight and accountability mechanisms would be a step in the right direction – it is unlikely we will be able to stop the runaway DoH train. But what should this look like? Who should have a say? And how would it work?
Academics, policy makers and civil society have been too disengaged from standards development, and now the impact is staring us in the face. The intersection of technology and policy is increasingly entangled. Those responsible for policy and human rights should increase their engagement in SDOs like the IETF to bring forward different perspectives early in development. They should also start earnestly working together to ensure DoH works for everyone, not just the big 5 tech companies and their partners.

